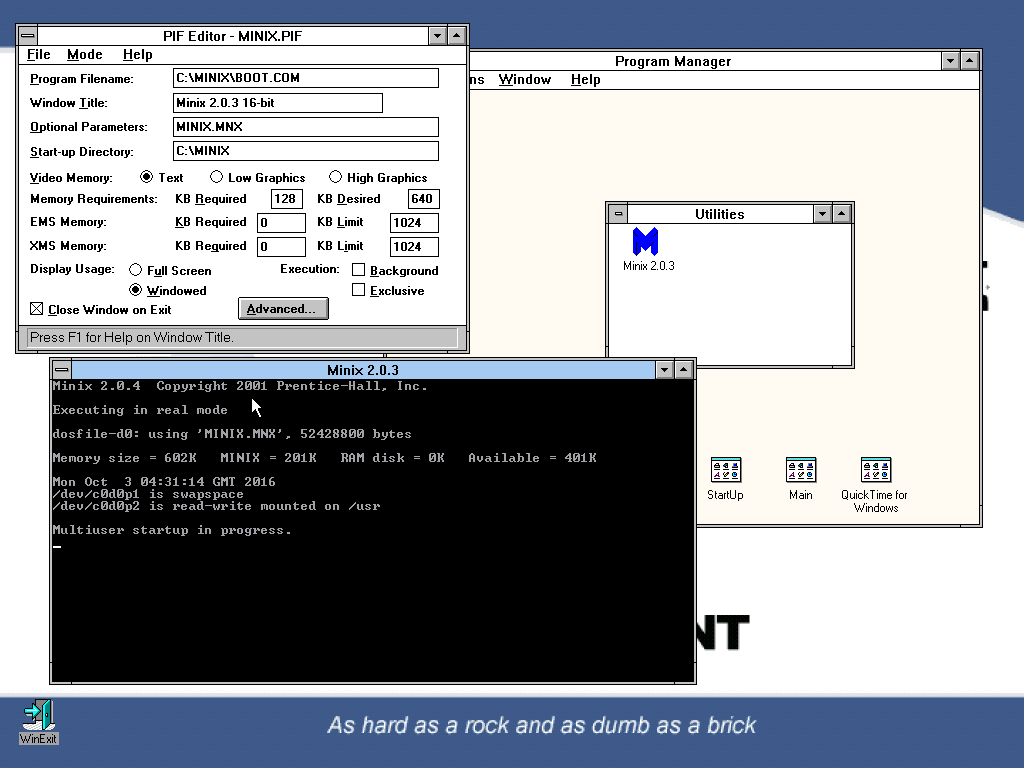
Sounds like you got it. It’s pretty fucking impressive actually. Intel are running their AMT system on a Minix stack in ring -3 (the lowest you’ll ever get to is ring 0 with a regular OS, and ring -1 if you’re accessing hardware VT-x/AMD-V virtualisation instructions; ring -2 is where UEFI lives) to corral management jobs and sensor data without bothering the OS that you’re actually intending to run on the CPU. Oh, and ring -3 isn’t even running on the CPU; there’s a separate CPU core in the same package (most recently, a 32-bit Intel Quark SoC).
The tricky bit is that there are now published vulnerabilities in the management stack, allowing password bypass to a system that includes capabilities such as remote consoles, both serial and graphical, a web interface to the management stack, and remote ISO mounting over emulated IDE or USB (depending on the age of the system).
So this is actually pretty fucking scary. But it doesn’t have to be. AMT is present on virtually every x86 CPU Intel have made for years, but it isn’t enabled by default on every x86 computer ever shipped. To be vulnerable, you need to have a “vPro” compatible system (supported CPU and chipset, supported network chipset), with the Intel AMT package installed in the BIOS, and with the AMT options enabled.
Let’s check some of my local systems to see if they’re nominally vulnerable …
neuro@intrepid:~$ neofetch | grep -e Host -e CPU | cut -d: -f2- && lspci | grep -e MEI -e HECI
10AW009QUK ThinkCentre E73
Intel i3-4150 (4) @ 3.500GHz
00:16.0 Communication controller: Intel Corporation 8 Series/C220 Series Chipset Family MEI Controller #1 (rev 04)
Yup …
neuro@mojave:~$ neofetch | grep -e Host -e CPU | cut -d: -f2- && lspci | grep -e MEI -e HECI
3237A1G ThinkCentre M92P
Intel i5-3470T (4) @ 3.600GHz
00:16.0 Communication controller: Intel Corporation 7 Series/C210 Series Chipset Family MEI Controller #1 (rev 04)
Yup …
neuro@memoryalpha:~$ neofetch | grep -e Host -e CPU | cut -d: -f2- && lspci | grep -e MEI -e HECI
HP ProDesk 400 G3 SFF
Intel i7-6700 (8) @ 4.000GHz
00:16.0 Communication controller: Intel Corporation Sunrise Point-H CSME HECI #1 (rev 31)
Aaaaaaaaaand yup.
But here’s the thing; I have management options disabled in BIOS on all of these machines. So they’re fine. There are additional steps you can take while your computer is switched on, such as firewalling TCP/UDP 16992 and 16993, and block them at your border as well for when your computer is switched off, but the important part is disabling the management systems in your BIOS.
And this isn’t even about anything mental like arbitrary code execution, it’s just a password bypass into the ME interface itself, rather than the lower level RTOS part (and this is where we find Minix again). Yes, they can fuck with your installed OS and bootloader, but … shit, that’s still really bad, right?
So. Turn off AMT. That’s it. You’re safe. From this, at least.